Best Selling Products
Exposing 3 super sophisticated email scams that trap many people
Nội dung
Cybercriminals today not only upgrade their attack methods but also take advantage of cutting-edge technologies such as artificial intelligence (AI) to create perfect, unpredictable and much more dangerous fraud scenarios.

For years, internet users have associated phishing emails with sloppy, misspelled messages, with content so “innocent” that it can be recognized at a glance. However, the age of technology has changed everything. Cybercriminals today have not only upgraded their attack methods but also taken advantage of cutting-edge technologies such as artificial intelligence (AI) to create perfect, unpredictable and much more dangerous phishing scenarios.
If you’re still taking email scams lightly, it’s time to realize that scammers are getting more professional. In this article, we’ll look at three of the most common new-generation email scams, how they work, and how you can protect yourself from them.
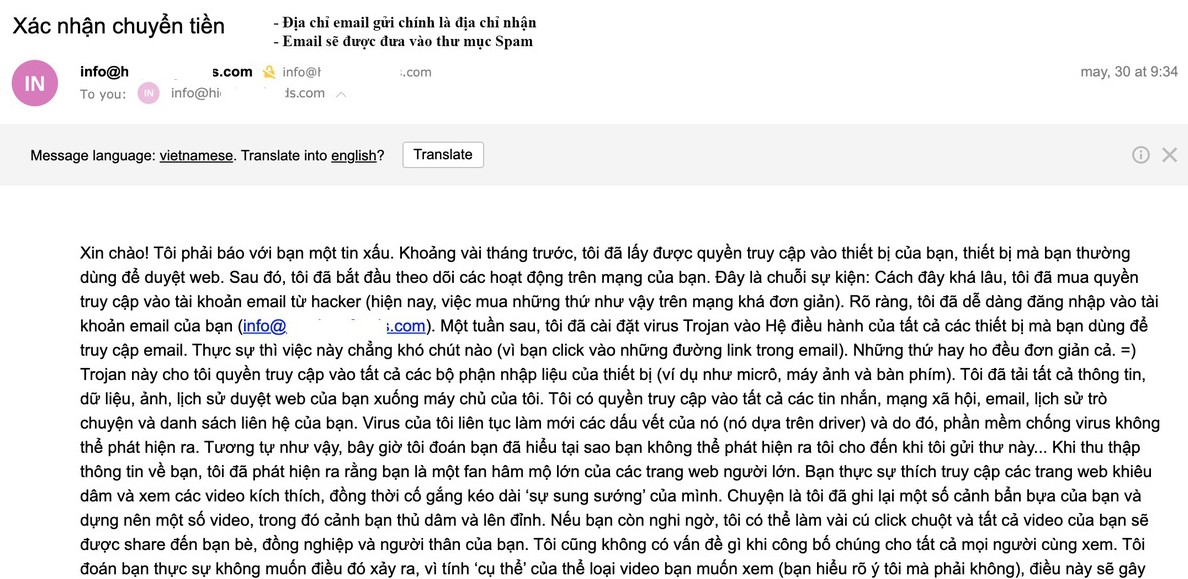
1. Blackmail with fear and sensitive videos
This is considered one of the most persistent, sophisticated and confusing scams. The scammer will send you an email that at first glance you can see it comes from your own address. The email content claims that they have successfully hacked your webcam and recorded sensitive video of you. To increase the level of fear, they threaten that if you do not pay the ransom (usually in cryptocurrency like Bitcoin) within 24-48 hours, the "sensitive" video will be sent to all your email contacts, even posted publicly on social networks.
What makes this tactic so convincing is that the scammer often includes some “evidence” to make it seem credible. They might include an old password you used (taken from a public data breach), or a Google Maps image of your house, and claim that they’re tracking your every move.
But the truth is, these guys don’t have any video at all. The technique of sending fake emails from your address is just a common trick among cybercriminals, and the exposed passwords actually come from previously leaked databases. They didn’t hack into your account.
The important thing when receiving these emails is to stay calm and collected. Don’t panic and don’t pay any money. Delete the email immediately. If you use the password in the email for other accounts, change it immediately and enable two-factor authentication (2FA) for added security. Also, remember that these emails are a sophisticated form of phishing designed to prey on fear. The more you panic, the more likely you are to fall for it.
2. “The bill fell from the sky”
Another common email scam that catches many people off guard is when you suddenly receive an email invoice or payment notification from a major e-commerce platform or online payment service. The email informs you that you have just purchased an expensive item such as a MacBook, a high-end phone, or an expensive security software package.
What makes many people panic is that these emails are extremely professionally designed, with logos, fonts, and layouts that are no different from real emails from large companies. The email content often includes a warning that if this is an invalid transaction, you need to immediately call the “support” phone number in the email to handle it.
However, this is the real trap. When you call the phone number in the email, the other end will be scammers posing as customer support staff. They will cleverly exploit your panic to continue a “social engineering” attack. The scammers will fabricate “problems” with your account or device, ask you to install remote control software to “fix the problem” or find a way to extract credit card information, ask you to provide OTP codes, or even transfer money directly to “solve the problem”.
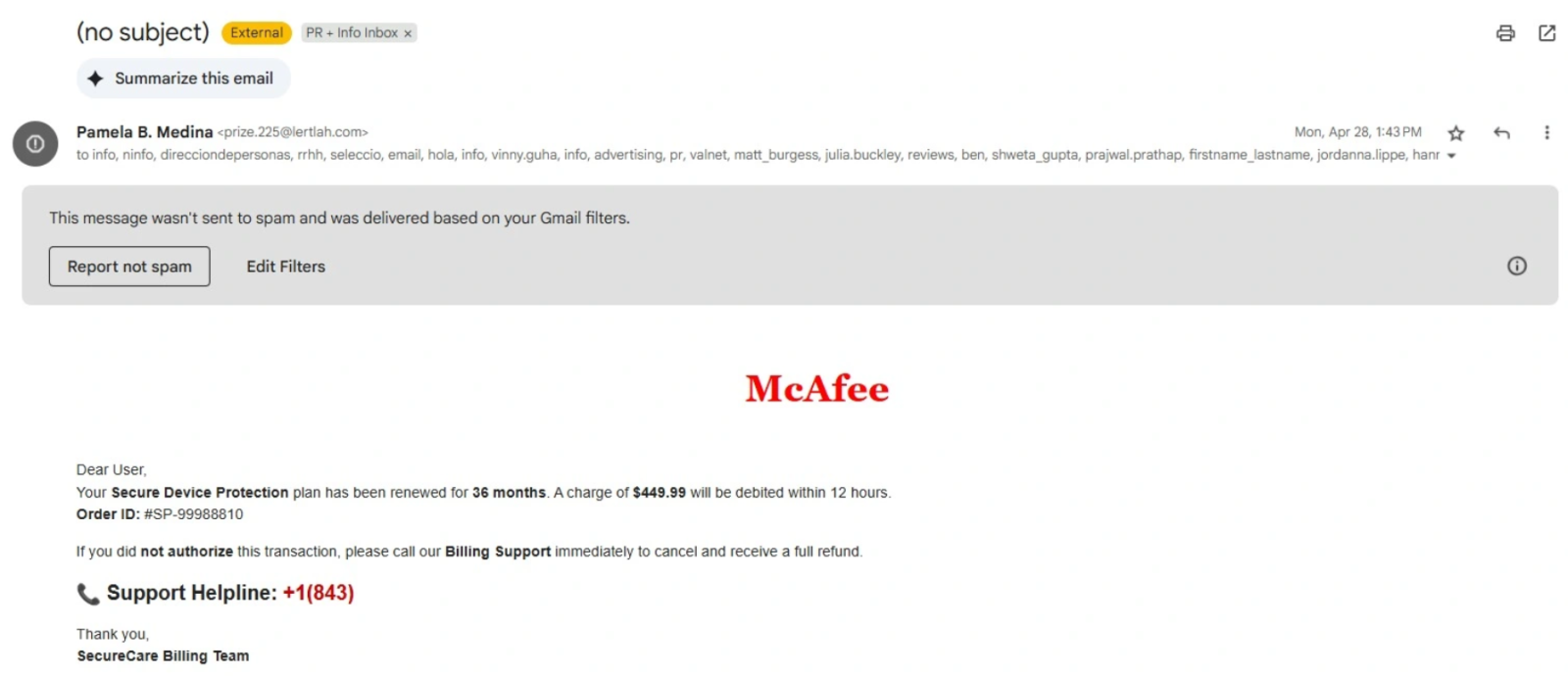
It is worth noting that this scam is not aimed at stealing the amount of money listed on the bill, but the real goal is to take control of your device or financial account. To avoid falling into this trap, remember: never call the phone number in an email that you are suspicious of. If you want to verify the information, go directly to the official website of the company mentioned in the email, or check your bank statement yourself. If the transaction is fake, nothing will appear in your account.
Additionally, there are some telltale signs of a fake invoice. They often lack information that a genuine invoice would have, such as the last four digits of the credit card you used, a detailed shipping address, or specific account information. The lack of these details is a sign that the email is not coming from a real company.
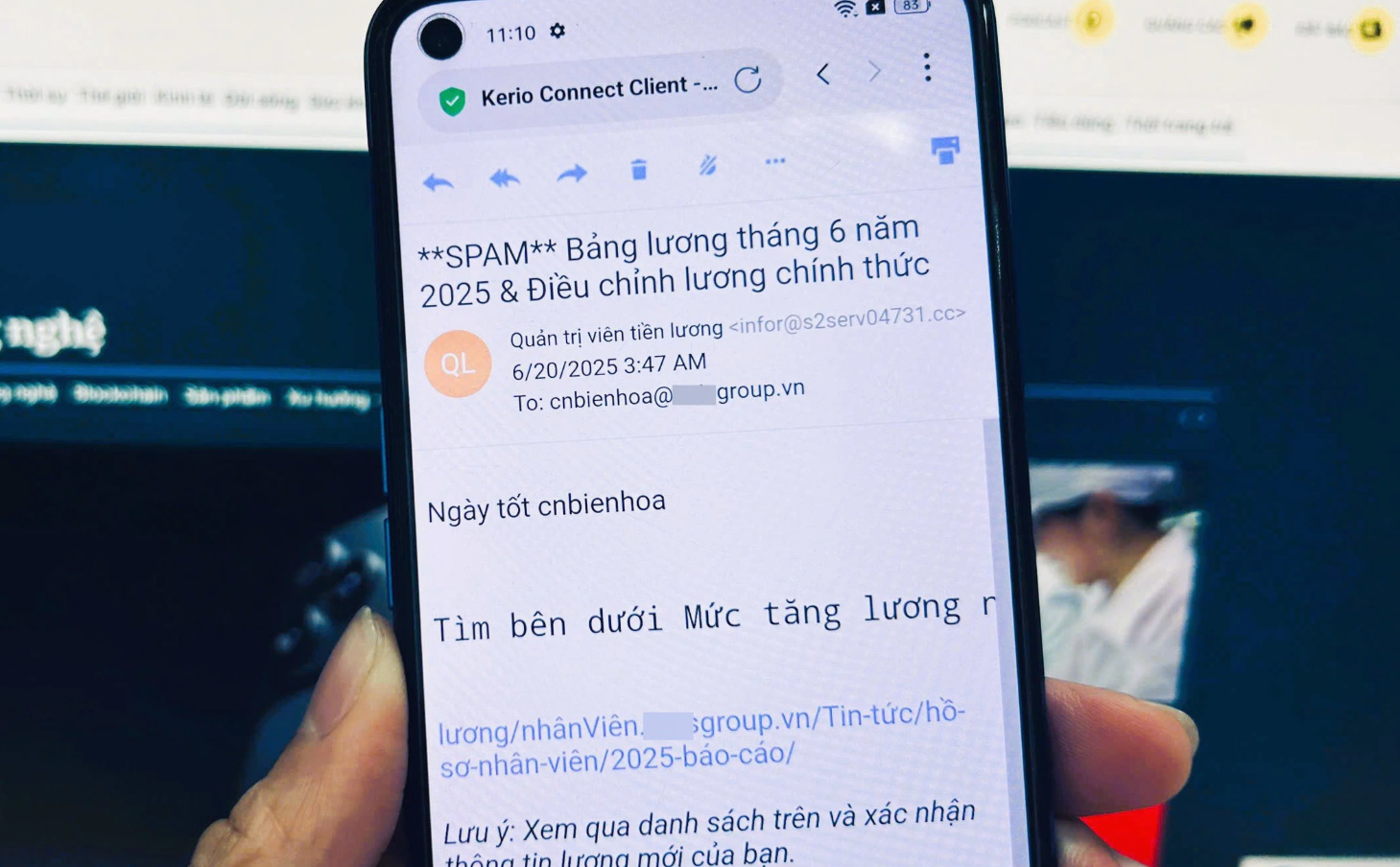
3. Phishing emails are taken to the next level
While in previous years we could easily spot phishing emails by looking for spelling, grammar, or sloppy writing, things have changed completely. Artificial intelligence is becoming a powerful tool for scammers, helping them craft more sophisticated and perfect emails than ever before.
AI eliminates the telltale signs of the past. Phishing emails are now polished, with no spelling errors or awkward phrasing. They are written in a natural style, even using the form of address, language, and style appropriate to the target audience.
AI can also create convincing fake images that go beyond text. For example, if a victim has posted about a lost pet on social media, the scammer can use AI to create a fake photo that shows they have “found” the pet and demand a ransom. This is a great example of AI being used to enhance the scam.
Another danger is that AI can scan and aggregate publicly available information about you on the internet and social media in seconds. Seemingly harmless information you share, such as the company you work for, the events you recently attended, or your friends, can all be exploited. Scammers can create emails impersonating your company’s human resources department and send you a “job satisfaction survey.” Or they can pretend to be a new friend they met at a recent event and send you emails containing malicious links.
The common thread in all forms of email scams is that they appeal to the emotions of their victims. No matter how sophisticated the scam, it always tries to incite fear, panic, or greed to make you act rashly. This is the vulnerability that scammers exploit.
4. Tips to protect yourself from sophisticated tricks
With scams becoming increasingly sophisticated, protecting yourself requires a high level of vigilance. Remember these principles:
Always stay calm when dealing with suspicious emails. Scammers often use panic, fear, or impatience to get you to do what they ask without thinking. Take a deep breath, read the content carefully, and consider the logic of the email before acting.
Never click on links or call phone numbers in unfamiliar emails. Links in phishing emails often lead to fake websites that can steal your account information or install malware on your device. If the email asks you to verify your information, type the official website address into your browser yourself; never click directly from the email.
Double-check the sender’s address. Don’t just look at the display name in the email, as it can be easily spoofed. Pay close attention to the domain name after the “@” to see if it matches the official domain name of the company or service the email is referring to. Even a single character difference (e.g. “amaz0n.com” instead of “amazon.com”) can be enough to tell that it’s a scam.

Update and change your passwords regularly, and enable two-factor authentication (2FA) for important accounts. Strong passwords should be long and include a combination of uppercase and lowercase letters, numbers, and special characters. 2FA adds an extra layer of protection, making it difficult for hackers to access your account even if your password is compromised.
Keep an eye out for data breaches so you can react quickly. You can use email breach checking services (like “Have I Been Pwned”) to see which of your accounts have been exposed. If you notice a breach, change your password immediately and activate the necessary security measures.
In addition to the above principles, be proactive in improving your knowledge of cyber security and sharing warning information with relatives and friends. Spreading awareness helps the community build a safer online environment, reducing the risk of being exploited by cyber criminals. Cyber criminals are constantly evolving and they are always finding new ways to exploit human weaknesses. But with vigilance and knowledge, you can completely protect yourself from the most sophisticated phishing emails. Don't let fear or subjectivity make you a victim.